Introduction
The modern Internet, accessible to billions worldwide, serves as a vast network, enabling everything from social connections to business transactions. What we see on our browsers—known as the Surface Web—is only a fraction of the Internet’s true scope. Beneath lies the Deep Web, a largely unindexed area used for private and institutional data, and further, the Dark Web, known for its encrypted, anonymous communications. This article delves into the hidden layers of the Internet, revealing their structures, roles, and significance while demystifying misconceptions and providing a guide for navigating and understanding these uncharted realms.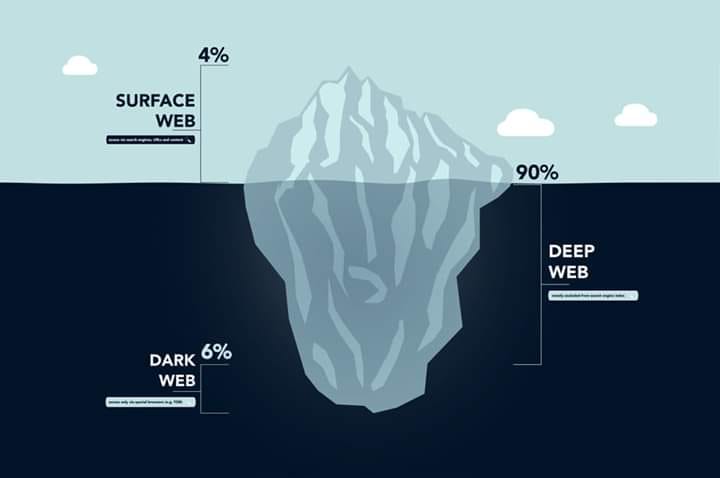
Chapter 1: The Surface Web – What Most of Us See
The Surface Web comprises the indexed content searchable on standard engines like Google, Bing, and Yahoo. It includes sites we use daily, like social media platforms, news outlets, e-commerce stores, and blogs, all searchable with standard keywords.
- Definition and Characteristics
- Publicly accessible, without special permissions
- Indexed by search engines for ease of access
- Examples and Applications
- Online shopping (Amazon)
- Social media (Facebook, Instagram)
- News and information sites (BBC, CNN)
- Limitations of the Surface Web
- Only represents 4–10% of the entire Internet
- Does not include private databases, academic journals, medical records, and proprietary information
Chapter 2: The Deep Web – The Vast Unindexed Landscape
The Deep Web contains information not indexed by standard search engines, accessible only with specific permissions or links. While the term may sound mysterious, much of the Deep Web is benign and used regularly by institutions and individuals.
- Definition and Scope
- Unindexed by search engines
- Access requires authentication, direct links, or specialized software
- Key Components
- Academic Databases: University libraries and research papers
- Medical Records: HIPAA-compliant databases with sensitive patient information
- Government Records: Confidential government databases not for public access
- Financial and Legal Data: Private client files and financial reports within banking systems
- Functionality and Security
- Offers enhanced privacy for secure transactions and sensitive data handling
- Reduces unauthorized access, often through secure login systems and firewalls
- Common Misconceptions
- Not Illicit: Often confused with the Dark Web, the Deep Web comprises primarily legitimate and secure data stores
Chapter 3: The Dark Web – A Subset of the Deep Web
The Dark Web operates as a tiny subset of the Deep Web, accessible through encrypted networks like Tor (The Onion Router) and I2P (Invisible Internet Project). Known for its potential to host illicit activities, the Dark Web also serves as a haven for privacy-focused communication and information exchange.
- Definition and Accessibility
- Accessible only through specialized software, typically with a higher degree of anonymity
- Uses layered encryption, routing requests through multiple nodes for obscured IPs
- Structure and Protocols
- Onion Routing: Conceals user identity through multiple layers of encryption
- Peer-to-Peer Networks: Further decentralizes access points, making tracking difficult
- Positive Uses of the Dark Web
- Privacy for Journalists and Activists: Communication for those in censored regions
- Whistleblowing Platforms: Secure exchange of sensitive information (e.g., SecureDrop)
- Research and Open-Source Knowledge: Provides a haven for anonymous collaboration in areas like cybersecurity
- Risks and Controversies
- Illegal Markets: Known for sites like Silk Road (shut down), where illegal items are sold
- Cyber Threats: Hosting of malware, phishing sites, and scams
- Reputation: Often equated with crime, despite legitimate uses
Chapter 4: Security and Ethics – Navigating Safely
Accessing the hidden layers of the Internet requires an understanding of the security tools, legal boundaries, and ethical implications.
- Encryption and VPNs
- Virtual Private Networks (VPNs): Mask IP address for added security on the Surface and Deep Web
- End-to-End Encryption: Essential for secure communication
- Legal Considerations
- International Law Compliance: Illegal activities are prosecuted across borders, even on the Dark Web
- Ethical Use: Professionals leverage hidden layers responsibly, balancing privacy with security
- Avoiding Malicious Threats
- Antivirus and Firewalls: Protect devices when accessing untrusted sources
- Awareness and Education: Knowing red flags, avoiding malicious sites
Chapter 5: The Future of Internet Privacy and Access
As Internet use evolves, the need for privacy, anonymity, and secure communication continues to grow. The hidden Internet layers will play a pivotal role in enabling secure and private exchanges while challenging international law enforcement.
- Advancements in Encryption
- Quantum encryption and blockchain solutions for even more secure data management
- Role of AI in Cybersecurity
- Detecting and preventing illicit activities with AI surveillance while maintaining ethical standards
- Legal and Ethical Implications
- Balancing transparency and user privacy for a more open yet secure Internet
Chapter 6: Tools and Technologies for Accessing the Deep and Dark Web
Accessing the deeper layers of the Internet requires specialized tools and software designed to preserve user anonymity and facilitate secure browsing. Below is an overview of the most commonly used tools for navigating beyond the Surface Web.
- Tor (The Onion Router)
- Purpose: Primarily used for anonymous browsing on the Dark Web
- How It Works: Routes Internet traffic through a series of nodes to conceal user IP addresses
- Applications: Accessing .onion sites, which are exclusive to the Dark Web, often for secure, anonymous communication
- I2P (Invisible Internet Project)
- Purpose: Decentralized, anonymous network designed for private data exchange and secure browsing
- Functionality: Uses end-to-end encryption and encrypted “tunnels” between peers to protect user identity
- Applications: Popular among those looking for more privacy; ideal for secure file sharing and hosting sites
- Freenet
- Purpose: Peer-to-peer platform that allows users to share files, chat on forums, and publish websites anonymously
- How It Works: Distributes data across its network of nodes to obscure both the source and the destination of data
- Applications: Used for storing sensitive information, distributing censorship-resistant content, and hosting privacy-oriented forums
- VPNs (Virtual Private Networks)
- Purpose: Securely tunnels Internet traffic and masks IP addresses on any part of the web
- Uses: Essential for adding a layer of anonymity on the Surface and Deep Web by routing through encrypted servers
- Popular Providers: ExpressVPN, NordVPN, and ProtonVPN, each with varied levels of encryption and speeds
Chapter 7: Privacy and Ethical Considerations for Users
Navigating the Internet’s hidden layers opens up questions of ethics and responsibility. Balancing privacy, anonymity, and ethical behavior is critical when accessing deeper Internet realms.
- User Responsibilities
- Data Security: Avoid sharing sensitive personal information, and always verify the integrity of downloaded content
- Respect for Privacy: Avoid exploiting the hidden layers for illegal activities or to harm others, even though these realms provide anonymity
- Ethical Usage
- Journalism and Research: Use hidden Internet layers responsibly for safe communication in restrictive countries
- Humanitarian Needs: Support causes by sharing legitimate, censored information securely, without compromising ethics
- Legal Boundaries
- Jurisdictional Challenges: While anonymity is achievable, many governments are increasingly monitoring the Deep and Dark Web for illegal activities
- Legal Compliance: Navigating responsibly includes understanding that accessing some types of data or engaging in certain actions can lead to prosecution
Chapter 8: The Risks Associated with the Dark Web
Though the Dark Web has valid uses, it’s also a hotspot for illegal activities, from the sale of counterfeit goods to data theft and cyber-attacks. Understanding these risks is crucial for anyone interested in exploring this area.
- Malware and Cyber Threats
- Common Threats: Trojans, keyloggers, ransomware, and spyware are prevalent and often hidden in files and links on the Dark Web
- Protection Tips: Avoid clicking suspicious links, ensure that antivirus software is up to date, and use secure systems for access
- Scams and Fraud
- Fraudulent Services: Many sites offer illegal services or “too good to be true” offers designed to exploit newcomers
- Prevention Tips: Avoid sharing personal or financial information and avoid interactions that seem untrustworthy
- Illicit Markets
- Dangerous Goods and Services: Some Dark Web marketplaces offer illegal substances, firearms, stolen data, and hacking tools, creating significant legal risks for visitors
- Awareness: Understand that even browsing such sites may be illegal in some jurisdictions, and purchasing illegal goods poses high legal risks
Chapter 9: The Role of Cybersecurity and Law Enforcement on the Hidden Web
Cybersecurity firms and law enforcement agencies actively monitor the Deep and Dark Web to prevent and address cybercrimes. From intercepting illicit transactions to preventing data leaks, these agencies play a key role in maintaining order in these hidden spaces.
- Cybersecurity Firms
- Threat Monitoring: Use algorithms and advanced software to track illegal activities and potential data breaches on the Dark Web
- Data Breach Alerts: Inform businesses and individuals when sensitive information like credit card numbers or passwords appears on illegal forums
- Law Enforcement Initiatives
- International Cooperation: Agencies like Interpol, the FBI, and Europol collaborate to address the challenges posed by the anonymous nature of the Dark Web
- Key Operations: High-profile takedowns of illegal marketplaces (e.g., Silk Road, AlphaBay) highlight law enforcement efforts to disrupt criminal activity
- The Role of Ethical Hackers
- White Hat Efforts: Ethical hackers often assist law enforcement by identifying and reporting vulnerabilities
- Educational Contributions: Many work with cybersecurity companies to improve Internet security measures and provide awareness on cyber hygiene
Chapter 10: The Future of the Internet’s Hidden Layers
The future of the Internet’s hidden layers will likely involve a complex interplay between privacy rights, emerging technology, and legal frameworks. Increased regulation and advancements in technology will continue to shape how users interact with these layers.
- Impact of Emerging Technologies
- Blockchain and Decentralization: Innovations in blockchain could redefine data storage and access, potentially decentralizing more data layers beyond current Dark Web applications
- Quantum Computing: The potential for quantum decryption poses new challenges, as it could break through encryption commonly used on the Deep and Dark Web
- Policy and Regulatory Evolution
- Balancing Privacy and Security: As governments enact stricter data protection laws, debates around the ethical usage of anonymous layers will likely intensify
- International Collaboration: Regulatory harmonization will be essential to manage illegal activities and enhance user protections across jurisdictions
- Public Awareness and Digital Literacy
- Education on Safe Internet Practices: With a growing emphasis on data security and privacy, educational programs will be crucial to help users understand responsible browsing practices across all Internet layers
- Privacy and Data Control Movements: Trends toward user-controlled data platforms are expected to rise, empowering users to take charge of their online privacy
Conclusion
The Internet’s hidden layers—comprising the Deep and Dark Web—are vast, complex, and filled with both opportunities and risks. While they serve critical purposes for privacy, secure data exchange, and information dissemination, these areas also present unique challenges. From understanding the legitimate uses of the Deep Web to navigating the ethical and legal implications of the Dark Web, users must be informed and cautious. The evolving landscape of Internet privacy, technology, and law enforcement will continue to shape the boundaries of these hidden layers, highlighting the importance of responsible and knowledgeable Internet usage for all.
More Informations

The Surface Web, the Deep Web, and the Dark Web constitute distinct layers of the internet, each characterized by unique features and functionalities. These layers collectively define the expansive landscape of the World Wide Web, encompassing a spectrum of accessible and hidden content.
The Surface Web, often referred to as the Clearnet or Indexed Web, constitutes the visible layer of the internet accessible through standard search engines like Google, Bing, or Yahoo. This segment comprises websites and web pages that are indexed, categorized, and easily accessible by conventional web browsers. Users can navigate the Surface Web effortlessly, exploring a myriad of information ranging from educational resources and news articles to e-commerce platforms and entertainment websites. The content on the Surface Web is designed to be readily available to the public, and its visibility is a result of indexing by search engine algorithms, making it a familiar and navigable space for the majority of internet users.
In contrast, the Deep Web represents a more extensive and less conspicuous portion of the internet, not indexed by traditional search engines. This realm encompasses a vast array of content, including databases, academic resources, private networks, and password-protected websites. The Deep Web is not inherently illicit or hidden; rather, its content requires specific credentials, permissions, or direct access to be reached. Examples of Deep Web content include subscription-based services, confidential corporate databases, and academic repositories, emphasizing the diversity and depth of this concealed layer.
Moving further into the opaque recesses of the internet, we encounter the Dark Web, a subset of the Deep Web distinguished by its intentional concealment and anonymity features. The Dark Web relies on encrypted networks such as Tor (The Onion Router) to ensure the privacy and anonymity of users. Unlike the Surface and Deep Web, which operate on the standard internet infrastructure, the Dark Web necessitates specialized software and configurations to access its content.
The Dark Web is notorious for hosting a variety of activities, ranging from privacy-centric communication platforms to illicit marketplaces trading in contraband goods and services. Cryptocurrencies, often Bitcoin, are commonly used for transactions on the Dark Web, contributing to the perceived anonymity of users engaged in activities therein. It is crucial to note that while the Dark Web has garnered attention for its association with illegal activities, it also serves as a refuge for individuals seeking privacy and secure communication in regions with restricted internet freedom.
The Surface, Deep, and Dark Webs collectively illustrate the multifaceted nature of the internet, catering to a spectrum of user needs and preferences. The Surface Web is the familiar face of the internet, easily navigable and indexed for public consumption. The Deep Web, while often misunderstood as a hub of secrecy, encompasses legitimate and private content that requires specific access protocols. The Dark Web, embedded within the Deep Web, introduces an element of anonymity, enabling both lawful privacy and, regrettably, illicit activities. Understanding these layers provides a comprehensive perspective on the internet’s complexity and the diverse ways individuals engage with its vast resources.
Delving deeper into the layers of the internet, the Surface Web, as the most visible stratum, encapsulates an extensive array of information, services, and interactive platforms. This encompasses everything from blogs, news websites, and educational resources to social media networks, e-commerce portals, and government websites. The content on the Surface Web is designed to be easily accessible to a global audience, shaping the digital landscape that many users encounter on a daily basis.
The Deep Web, on the other hand, comprises a reservoir of information that isn’t indexed by traditional search engines, resulting in its relative obscurity. This vast expanse includes proprietary databases, private email accounts, academic databases, and subscription-based content. The Deep Web isn’t inherently secretive or malicious; rather, it accommodates content that requires specific access permissions, such as academic databases or confidential corporate intranets. The Deep Web, thus, represents a significant portion of the internet that is not immediately visible but serves critical functions in areas like research, commerce, and secure data storage.
Navigating further into the layers of obscurity, the Dark Web stands out as a realm designed explicitly for anonymity and privacy. Operating on overlay networks like Tor, which routes internet traffic through a series of volunteer-operated servers to conceal a user’s location and usage from network surveillance or traffic analysis, the Dark Web allows individuals to access websites with “.onion” domain extensions. These sites, intentionally hidden from standard search engines, range from forums and communication platforms to marketplaces offering various goods and services, both legal and illicit.
The anonymity afforded by the Dark Web has led to its association with certain illicit activities, including the sale of drugs, hacking tools, stolen data, and other illegal commodities. Cryptocurrencies, primarily Bitcoin, are often the preferred medium of exchange in these transactions due to their decentralized nature and potential for enhanced privacy. It is crucial to emphasize, however, that the Dark Web also serves legitimate purposes, providing a platform for whistleblowers, activists, and individuals in oppressive regimes to communicate securely without fear of retribution.
In terms of technological infrastructure, the Surface Web relies on the standard internet architecture, with content hosted on servers and accessed through direct URLs or search engine queries. The Deep Web, by contrast, includes content that is dynamically generated, requiring user inputs or specific authentication for access. Encryption protocols and secure connections are prevalent in the Deep Web to safeguard sensitive data.
The Dark Web introduces additional layers of complexity by utilizing overlay networks like Tor, I2P (Invisible Internet Project), or Freenet, which enable users to access “.onion” websites while concealing their identity. These networks prioritize privacy and anonymity, creating a unique digital environment that, while associated with some nefarious activities, also facilitates lawful endeavors.
In conclusion, the internet’s layers, from the easily accessible Surface Web to the less visible but crucial Deep Web and the intentionally concealed Dark Web, present a nuanced and intricate ecosystem. Recognizing the distinct characteristics of each layer is essential for a comprehensive understanding of the internet’s capabilities, challenges, and the diverse ways in which individuals and organizations engage with its vast resources.
Keywords
- Surface Web:
- Explanation: The Surface Web, also known as the Clearnet or Indexed Web, constitutes the visible layer of the internet that is easily accessible through conventional search engines. It includes websites and web pages that are indexed, categorized, and readily available to the public.
- Interpretation: The Surface Web is the part of the internet that most users interact with daily. It encompasses a vast range of content, from informational sites to e-commerce platforms, and is easily navigable through standard web browsers.
- Deep Web:
- Explanation: The Deep Web represents a larger, less visible portion of the internet that is not indexed by traditional search engines. It includes content that requires specific access credentials, such as academic databases, private networks, and password-protected websites.
- Interpretation: The Deep Web is often misunderstood as a secretive space, but it primarily consists of legitimate and private content. It caters to a variety of needs, including research, confidential corporate data, and subscription-based services.
- Dark Web:
- Explanation: The Dark Web is a subset of the Deep Web characterized by intentional concealment and anonymity features. It relies on encrypted networks like Tor to ensure user privacy. While it hosts privacy-centric communication platforms, it’s also known for illegal activities such as the sale of contraband goods on illicit marketplaces.
- Interpretation: The Dark Web introduces an additional layer of privacy and anonymity, allowing users to engage in activities away from conventional scrutiny. While it has lawful applications, it has gained notoriety due to its association with illicit transactions and services.
- Tor (The Onion Router):
- Explanation: Tor is a privacy-focused network that enables anonymous communication by routing internet traffic through a series of volunteer-operated servers. It is widely used to access the Dark Web, allowing users to conceal their location and online activities.
- Interpretation: Tor is a crucial technology for those seeking enhanced privacy on the internet. While it facilitates secure communication and access to the Dark Web, it has both lawful and unlawful applications.
- Cryptocurrencies:
- Explanation: Cryptocurrencies, such as Bitcoin, are decentralized digital currencies that use cryptography for secure financial transactions. They are often used on the Dark Web for their potential to provide enhanced privacy in transactions.
- Interpretation: Cryptocurrencies offer a decentralized and private means of financial transactions. While they have legitimate uses, their anonymity features have made them attractive for transactions on the Dark Web.
- Overlay Networks:
- Explanation: Overlay networks, like Tor, I2P, or Freenet, provide a layer of abstraction over the standard internet, enabling users to access specific content or websites with enhanced privacy and anonymity.
- Interpretation: Overlay networks add an extra layer of complexity to internet architecture, allowing users to navigate hidden services or content while maintaining privacy. They are instrumental in shaping the characteristics of the Dark Web.
- Encryption Protocols:
- Explanation: Encryption protocols are algorithms that transform data into a format that is unreadable without the correct decryption key. They are widely used in the Deep Web and Dark Web to secure sensitive information and communications.
- Interpretation: Encryption protocols play a crucial role in safeguarding information in hidden layers of the internet. They contribute to user privacy and data security, preventing unauthorized access to sensitive content.
Understanding these key terms provides insight into the intricate layers of the internet, highlighting the diverse functionalities, privacy considerations, and the coexistence of both legitimate and illicit activities within these digital realms.
